Difference between ACL and uniform bucket-level access in Google Cloud Storage
Start your free 7-days trial now!
In the context of Google Cloud Storage (GCS), both ACL (access control list) and uniform bucket-level access govern who has access to the objects stored in GCS as well as the level of access they have. This article goes over notable differences between the two access controls.
ACL offers more granular access control
As discussed in our getting started with GCS guide, objects such as text files and images are all stored under buckets. The main difference between ACL and uniform bucket-level access is that ACL allows for granular permission control on individual objects using ACL while uniform bucket-level access only allows you to grant permissions on individual buckets.
For instance, suppose we have a cat.png and a dog.png inside a bucket on GCS. With ACL, we can make cat.png accessible to the public while making dog.png private. In contrast, uniform bucket-level access only allows you to make all objects under the bucket either public or private.
Uniform bucket-level access is part of IAM but ACL is not
IAM (Identity and Access Management) is used across the suite of services offered by Google Cloud Platform (e.g. Cloud SQL and BigQuery) to administer permissions on who can use these services and what they can do with them. The uniform bucket-level access is a part of IAM whereas ACL is not. To allow for granular permission settings at an object-level, ACL was introduced uniquely to GCS. This means that IAM features like roles and service accounts can be used for uniform bucket-level access, but these cannot be used for ACL.
ACL and uniform bucket-level access cannot be used at the same time
When we enable uniform bucket-level access on GCS, ACL will automatically be disabled. This means that we cannot use uniform bucket-level access and ACL at the same time - you either use one or the other.
Once we enable uniform bucket-level access, and if active for 90 days, then this setting will become permanent. In other words, we cannot change from uniform bucket-level access to ACL after 90 days of using uniform bucket-level access. Within this 90-day window, GCS will keep your ACL settings - though they are disabled - just in case you wish to revert back to ACL.
On the other hand, we can always switch from ACL to uniform bucket-level access at any time.
When should we use ACL and when should we use uniform bucket-level access?
In general, Google recommends uniform bucket-level access whenever possible because this greatly simplifies having to manage granular permissions on the object-level. Also, uniform bucket-level access is a part of IAM while ACL is not, which means that uniform bucket-level access comes with features such as roles and service accounts, which you may already be familiar with if you use other GCP products. For these reasons, uniform bucket-level access is enabled by default instead of ACL when creating buckets.
It is good practice to structure our objects such that we place objects that require the same permission settings in the same bucket (uniform bucket-level access). The only need for ACL is when you have to set permissions to each object individually.
Enabling ACL or uniform bucket-level access on web Google Cloud Storage console
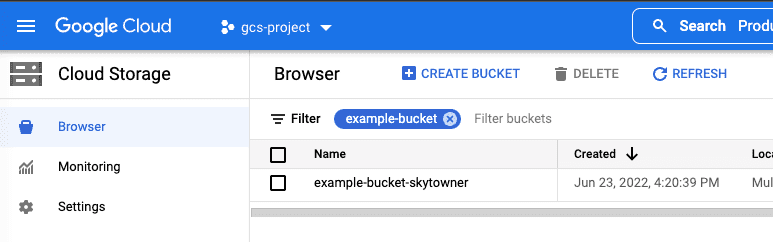
To enable ACL or uniform bucket-level access for a particular bucket, head over to the web GCS console, and click on the target bucket:
Next, click on the PERMISSIONS tab:
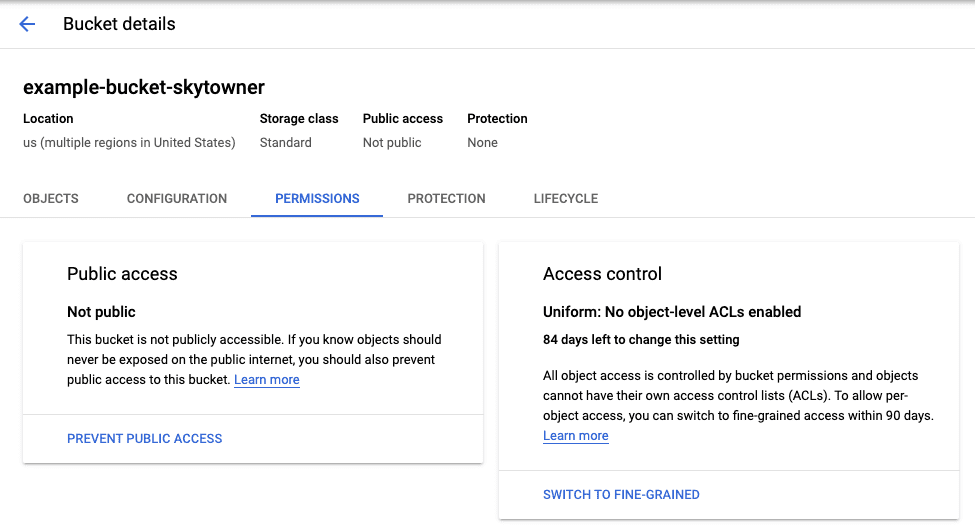
Here, we can see from the bottom right card that the access control of this bucket is set to uniform bucket-level access. We also see that we still have 84 days to switch to ACL - otherwise the access control of the bucket will permanently be set to uniform bucket-level access.
To switch from uniform bucket-level access to ACL, click on the SWITCH TO FINE-GRAINED button in the bottom right. The following dialogue will open up - Fine-grained here represents ACL:
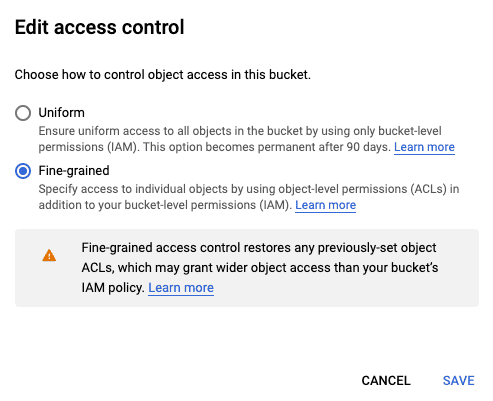
Hit SAVE and we should see the console update to ACL:

Prevent access prevention
We also have the option of enabling Prevent Access Prevention for buckets. With the Prevent Access Prevention enabled, files residing in this bucket cannot be publicly accessed and will throw a HTTP error regardless of our ACL or uniform bucket-level access settings. Note that this option can be enabled or disabled at any time.







