Creating a service account and private JSON keys in Google Cloud Platform
Start your free 7-days trial now!
What are service accounts in Google Cloud Platform?
Service accounts can be thought of as accounts used to access services on Google Cloud Platform (GCP) such as Google Cloud Storage and App Engine. When creating service accounts, we can select what services the account can interact with as well as the extent to which they can do so. For instance, we can create a service account that can only read files on Google Cloud Storage but cannot perform other operations like writing.
Service accounts can always be temporarily disabled or deleted at any time through the GCP web console or a client library. By doing so, users who were using the service account will no longer have access to the tied GCP resources.
Creating service accounts on Google Cloud Platform console
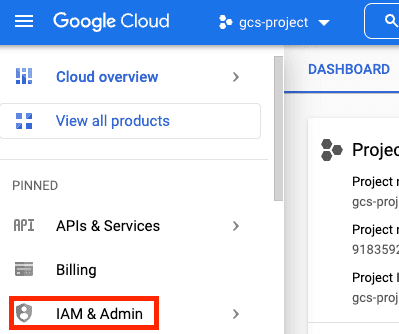
To create a service account, head over to IAM & ADMIN on the left sidebar:
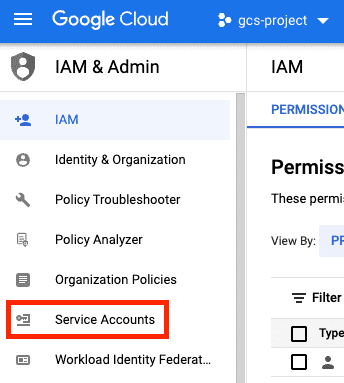
Next, click on Service Accounts:
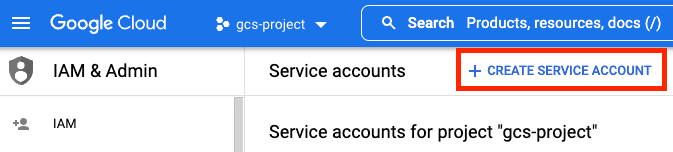
Next, click on CREATE SERVICE ACCOUNT:
Now, fill in the required forms:
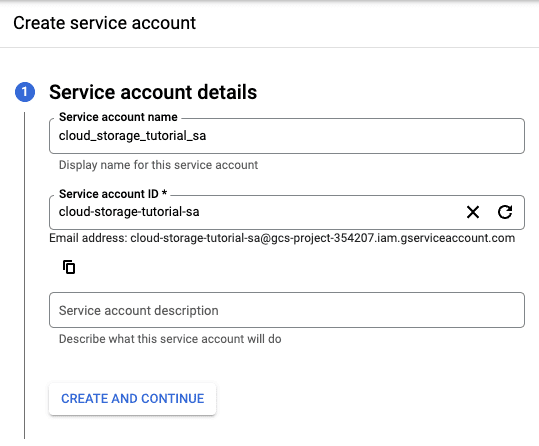
Here, we've created a service account called cloud_storage_tutorial_sa.
For the second step, we must grant privileges to the service account such that the service account is authorized to interact with certain Google services. For the purpose of experimenting with any service on GCP like GCS, we can grant the role of Editor under Basic to our service account:
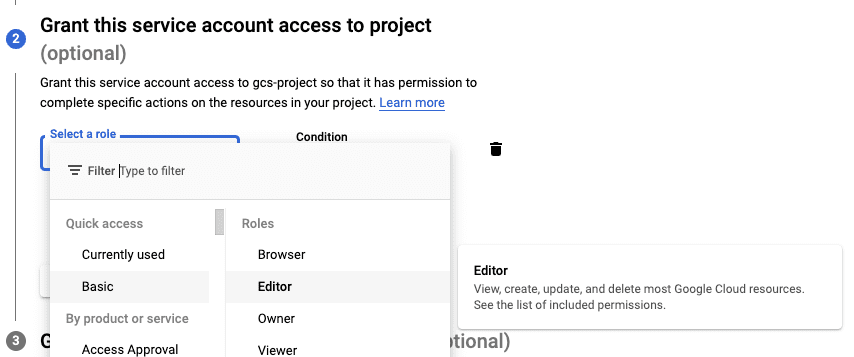
Make sure you limit the role to what the service account minimally requires in a production setting. The Editor role is a superuser role that allows the service account to basically do anything - like deleting all the files in GCS!
For the last optional step, you can specify which users have access to this service account:
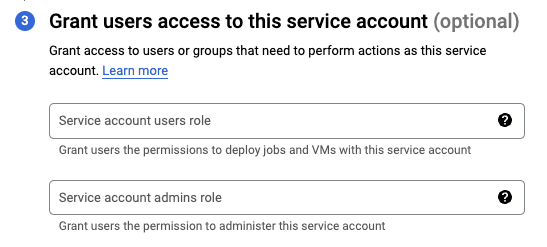
For instance, suppose you are an admin of your company and you want your employees to have read access to resources stored in Google Cloud Storage within GCP console. You can add their e-mail addresses, and they would be able to impersonate (act as) the service account. If you're just starting out, then you can leave this section blank and proceed to create the service account.
Creating a JSON private key of a service account
When using client libraries to interact with GCP services, we typically need to authenticate ourselves with a specific service account. Instead of using usernames and passwords to identify a service account, we use a private key, which is a JSON file holding the credentials of the service account. Anyone with this private key will be able to assume the role of the service account.
For instance, to insert a new file in Google Cloud Storage using the Python client library, we must pass in the credentials of the service account using a private key (JSON file):
from google.cloud import storagepath_to_private_key = './gcs-project-354207-099ef6796af6.json'client = storage.Client.from_service_account_json(json_credentials_path=path_to_private_key)
In this section, we will go over how to generate this private key so that you can authenticate yourself with a service account and gain access to GCP resources in client libraries.
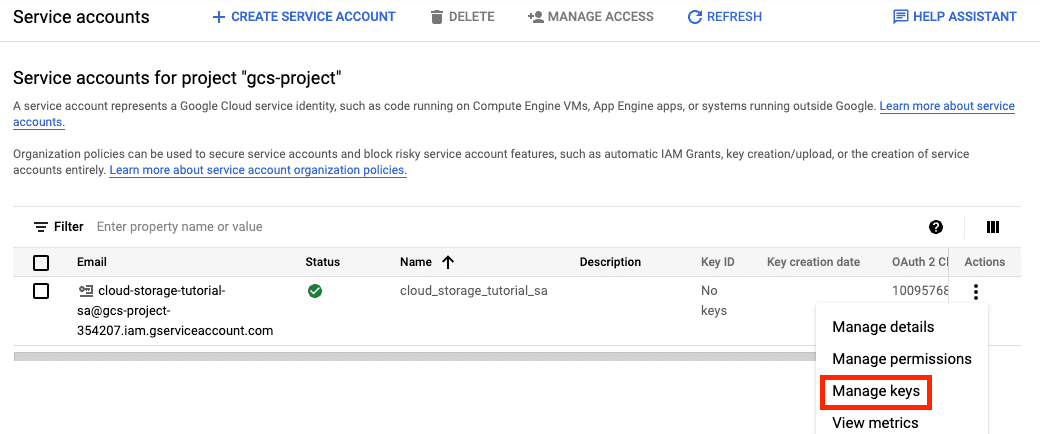
Head over to the Service accounts page on GCP, and then locate the service account of which to create the private key. Next, click on the three vertical dots under Actions, and then click on Manage Keys:
Next, click on ADD KEY and then Create new key:
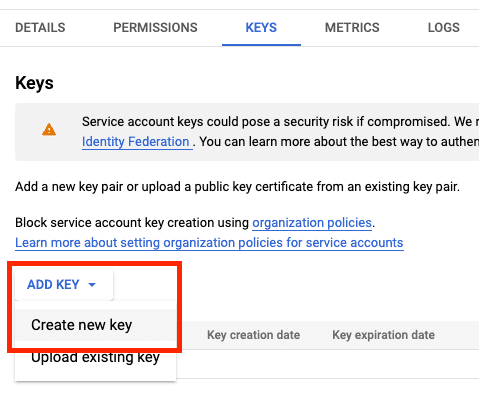
Next, select JSON (default) and click on CREATE:
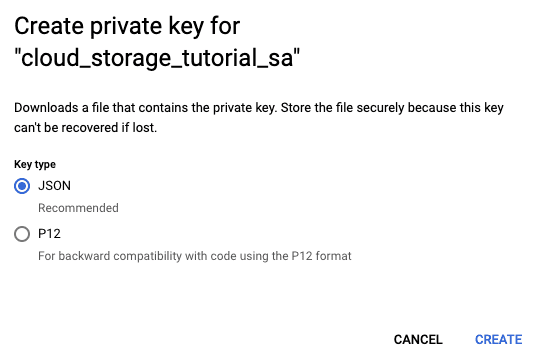
This should download a JSON file holding the required credentials!
The private key (the JSON credential file) is sensitive - do not share the file with anyone else because the private key allows them access to your GCP resources. Be particularly cautious when uploading files to a public repository on GitHub!







